IBM Security Verify Access
4
19
Access management and multifactor authentication to help businesses maintain security.
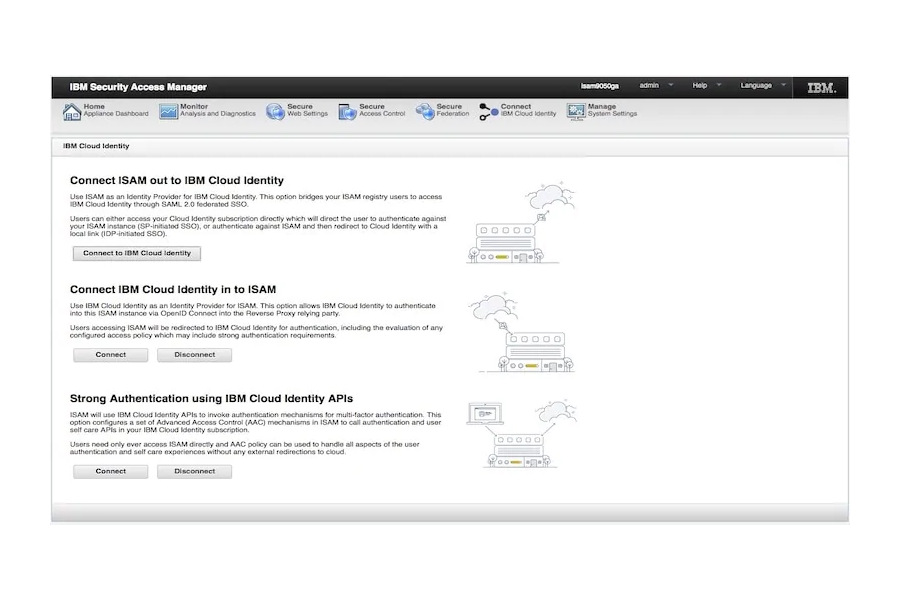
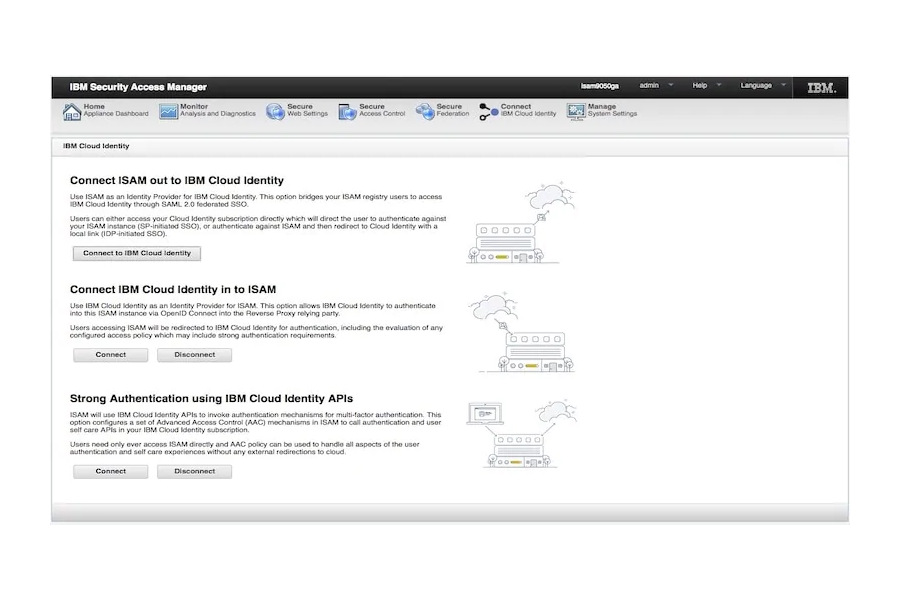
IBM Security Verify Access, formerly IBM Security Access Manager or ISAM, helps you simplify your users' access while more securely adopting web, mobile, IoT and cloud technologies. It can be deployed on-premises, in a virtual or hardware appliance or containerized with Docker. Verify Access helps you strike a balance between usability and security through the use of risk-based access, single sign-on, integrated access management control, identity federation and mobile multi-factor authentication. Take back control of your access management with Verify Access.
Ask anything of IBM Security Verify Access with Workflos AI Assistant
Apolo
Squeak squeak, I'm a cute squirrel working for Workflos and selling software.
I have extensive knowledge of our software products and am committed to
providing excellent customer service.
What are the pros and cons of the current application?
How are users evaluating the current application?
How secure is the current application?
Media